In todays environment, identity theft and related crimes are frequent and common place. Most of these incidents take place because our identity can be easily stolen will little bits of information such as name, address, birthdate, social security number or maybe just your card number.
What if, credit file or credit report or credit score even credit cards had two factor authentication, just like we have, two factor authentication on gmail, chase and many other services.
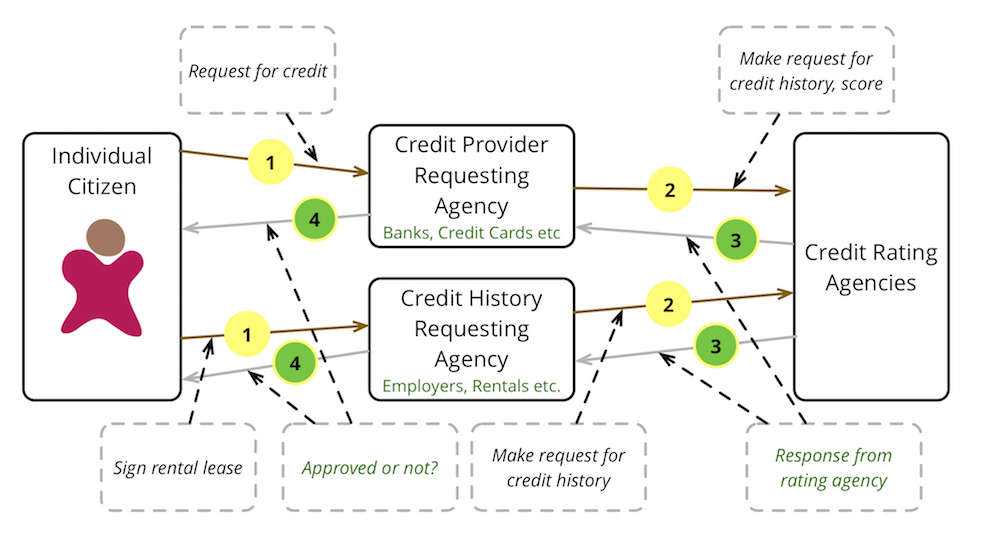
In the diagram above when an Individual Citizen makes an application to get a loan or rent an apartment, this action creates the following flow of information
- The application the individual fills, has personal identifying information and is submitted to the institutions providing the loan or the rental.
- These institutions in turn make a request to the credit rating agencies with all the personal information.
- The credit agencies, using the personal information look up the credit history and calculate the score for the individual and return the response with the credit history and/or score.
- The institutions now can determine based on the credit history and/or score, if to proceed with the transaction and determine the rate of interest or other parameters.
In the whole chain on events there is an implicit assumption that the individual making the request is the owner of the personal information being submitted, when the individual making the request is not the owner of the personal information identity theft credit card theft take place.
As a technology person that has grown to like two factor authentication I wonder why cannot it be applied to transactions involving credit card, credit files, credit history and identity related information.
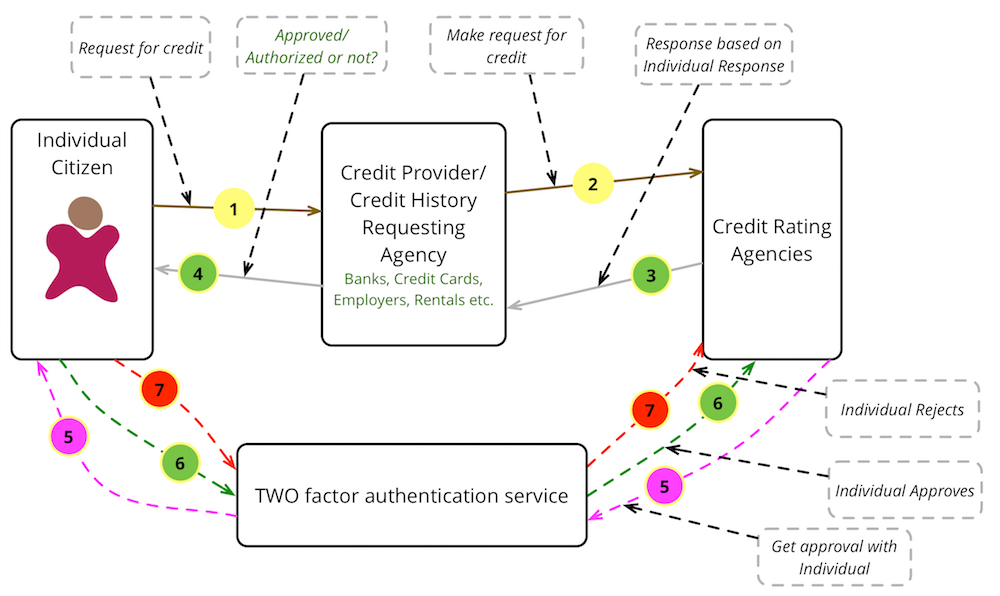
In the diagram above when an Individual Citizen makes an application, the credit agencies or the credit information requesting organizations can/should get conformation from the Individual Citizen via an alternate method such as SMS, EMAIL, Smart Phone App, Phone call or any other mode of communication.
Once the Individual Citizen approves the request as valid and initiated by them, the request should be fulfilled with valid data, if the Individual Citizen rejects the request as invalid or notifies that it was not initiated by them then the request can be rejected without putting the Individual Citizens information at risk.
Two factor authentication is very beneficial for the financial and other organizations as it increases the trust level of the transaction and reduces their losses because of stole identity. The Two factor authentication service can be implemented by either an independent organization or the credit rating agencies with enough independent information about the individual people.
